Juniper Crack Password
Def makepass ( user, password ): middle = 'Administration Tools' s = '%s:%s:%s'% ( user, middle, password ) print s m = hashlib. Kudos 2 Free Full Version Torrent. Digest ( ) narray = [ ] for i in range ( 8 ): n1 = ord (m [ 2*i ] ) n2 = ord (m [ 2*i+ 1 ] ) narray. Append ( (n1 >12 & 0xf p2 = i >>6 & 0x3f p3 = i & 0x3f res + = b64 [p1 ] + b64 [p2 ] + b64 [p3 ] for c, n in zip ( 'nrcstn', [ 0, 6, 12, 17, 23, 29 ] ): res = res [:n ] + c + res [n: ] return res After looking through the code it is clear that there is a fixed salt of Administration Tools and a salt of the username(lines 2 and 3).

The password protecting one of the two Juniper backdoors was published after it was discovered by researchers at Fox-IT and Rapid7. The password protecting one of the two Juniper backdoors was published after it was discovered by researchers at Fox-IT and Rapid7. Download Aplikasi Auto Tune Exe Versi Baru.
The code then takes each 2 chars and adds the binaries together(lines 8-11) From this it creates 3 characters from the 16bits(lines 14-18) And finally is scatters the letters n,r,c,s,t & n onto the hash in specific places (lines 20 and 21) It’s worth noting that the letters nrcstn is actually Ne TSCRee N in reverse without the e’s 🙂 Using this code it was possible to write some new code to reverse backwards through the steps in order to go from a Netscreen hash back to the raw MD5 hash. Here’s the function for this. Def reversetomd5 (knownhash ): # strip out nrcstn fixed characters clean = ' for i in [ 1, 2, 3, 4, 5, 7, 8, 9, 10, 11, 13, 14, 15, 16, 18, 19, 20, 21, 22, 24, 25, 26, 27, 28 ]: clean+ =knownhash [i ] # create blocks block = [ ] for i in xrange ( 2, 24, 3 ): p1 = b64. Index (clean [i- 2 ] ) p2 = b64.
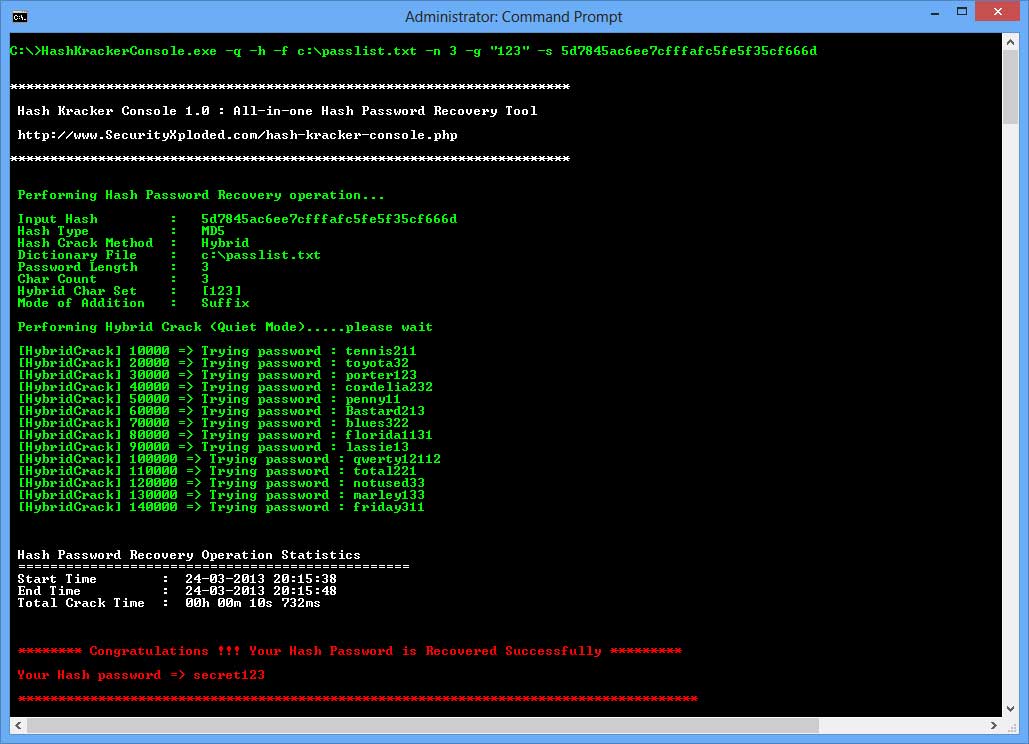
Index (clean [i- 1 ] ) p3 = b64. Index (clean [i ] ) block. Append (p1 >8 n2 = i & 0xff md5hash+ = chr (n1 )+ chr (n2 ) return binascii. A Note Centurion C 8416 Driver Download. Hexlify (md5hash ) Using this function you are able to give it a Netscreen hash and you’ll get back the raw MD5. C: cudaHashcat64.exe -m 20 netscreen.txt rockyou.txt cudaHashcat v1.01 starting.